Federal Authorities Dismantle LeakBase in Global Cybercrime Operation
Federal investigators have shut down LeakBase, an online hacker forum known for selling and hosting user information stolen in past data breaches. The takedown was led by the United States, with support from Europol, marking a coordinated international effort against cybercrime infrastructure.
As part of the operation, US authorities seized a LeakBase database containing user information. According to the Justice Department, the seizure provides investigators with valuable data that may help identify individuals involved in illegal cyber activities. Europol confirmed its participation and noted that investigators de-anonymized multiple users believed to be active cybercriminals.
By December 2025, LeakBase had grown significantly, with more than 142,000 registered users, approximately 32,000 posts, and over 215,000 private messages. Europol highlighted these figures to underscore the forum’s scale and global reach.
LeakBase’s Role in Selling Stolen Data and Compromised Credentials
Open-Web Accessibility via LeakBase Domains
LeakBase emerged in 2021 and operated openly on the web through domains such as leakbase[.]ws and leakbase[.]la. Unlike some cybercrime platforms hosted exclusively on the dark web, LeakBase was accessible through standard internet domains, broadening its reach and user base.
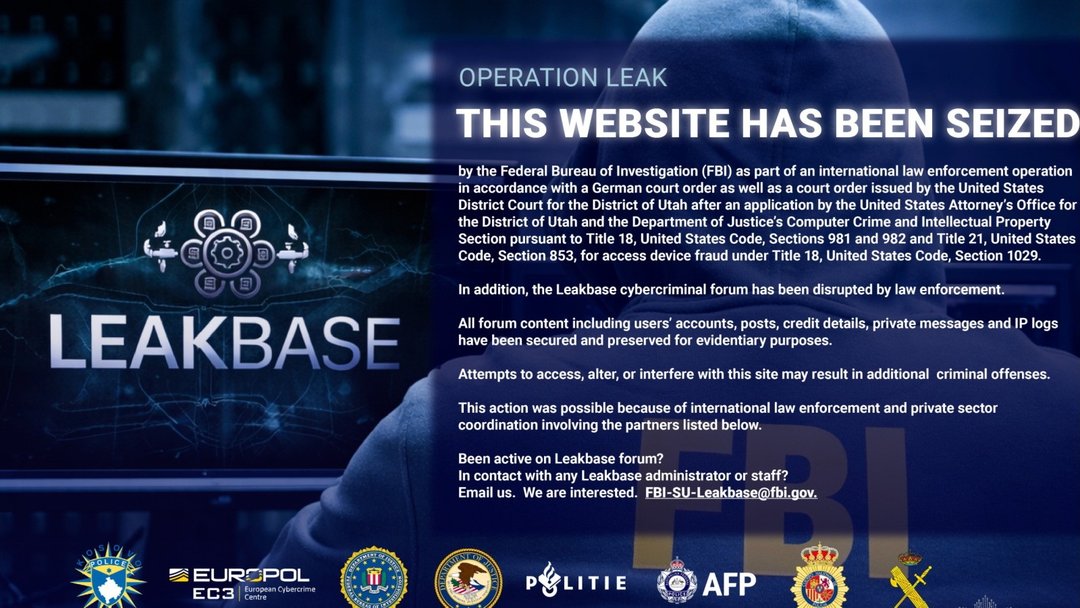
US authorities have since taken control of both domains, which now display a seizure notice, effectively disabling public access to the platform.
Hosting Hundreds of Millions of Stolen Account Credentials
Investigators report that LeakBase hosted numerous databases containing hundreds of millions of account credentials. These credentials were sourced from previous data breaches and malware campaigns, making the forum a centralized marketplace for compromised information.
The availability of such extensive datasets made LeakBase a valuable resource for cybercriminals seeking to conduct further attacks, including account takeovers and fraud schemes.
Sale of Financial and Personally Identifiable Information
According to the Justice Department, LeakBase allowed users to sell information from stolen databases, including data illegally obtained from US corporations and individuals. The marketplace included:
- Credit and debit card numbers
- Banking account and routing information
- Usernames and associated passwords
- Sensitive business information
- Personally identifiable information (PII)
This type of data can facilitate identity theft, financial fraud, and additional unauthorized access to online accounts. The aggregation and resale of such information amplified the impact of previous data breaches.
International Law Enforcement Actions Against Active Users
De-Anonymization and Enforcement Measures in Multiple Countries
Europol reported that authorities took action against 37 of the most active LeakBase users. These measures included arrests, house searches, and “knock-and-talk” interventions. The enforcement activities spanned multiple countries, including:
- United States
- Australia
- Belgium
- Poland
- Portugal
- Romania
- Spain
- United Kingdom
The coordinated approach reflects the transnational nature of cybercrime and the growing collaboration between global law enforcement agencies.
Suspected Russian Origins and Forum Rules
Security researchers have suspected that LeakBase originated from Russia. Europol noted that one of the forum’s internal rules prohibited the sale or publication of data related to Russia. This restriction has raised questions about the administrators’ location and potential protection from local enforcement.
Despite the takedown, the suspected administrators are believed to remain at large.
Implications for Cybersecurity and Future Hacker Forums
The United States has previously dismantled major hacker forums, demonstrating a pattern of targeting cybercrime marketplaces. However, history suggests that new platforms may emerge to replace those that are seized.
The FBI’s Cyber Division emphasized that the operation sends a clear message: no criminal is truly anonymous. By seizing the forum’s database and de-anonymizing users, authorities aim to deter participation in similar illicit marketplaces and disrupt the broader cybercrime ecosystem.