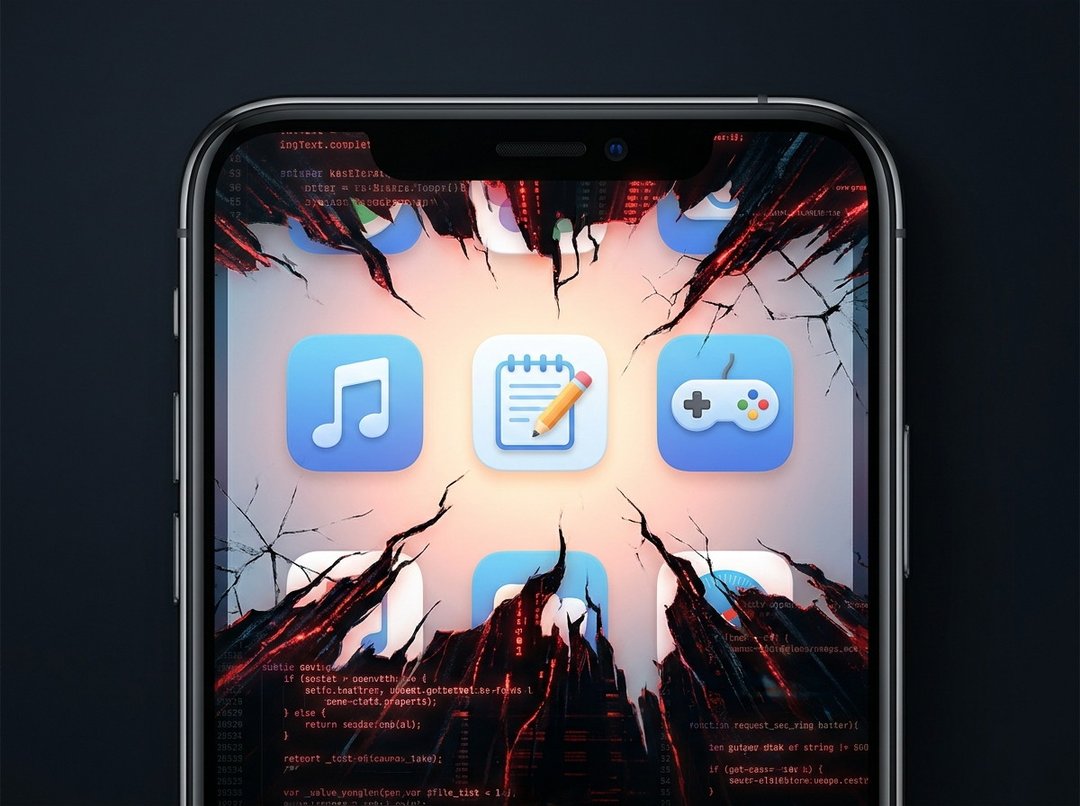
You're careful. Really careful. You don't click sketchy links in emails. You only install software from established storefronts like Microsoft or Steam. You check reviews before adding any browser extension. You do everything right — and yet, your PC could still get infected with malware.
That's not a scare tactic. That's just where things stand right now.
How Legitimate Software Becomes a Malware Delivery Vehicle
Here's the uncomfortable truth: hackers don't always need to trick you into downloading something shady. They can simply take over software you already trust and push malicious updates directly to your machine. You accept the update, your antivirus doesn't flag anything unusual (because the update appears to come from a legitimate source), and suddenly something nasty is sitting quietly on your PC.
This method of attack used to be rare enough that it made headlines when it happened. Back in 2017, when the popular PC utility CCleaner was compromised, the incident became notorious partly because it was so unusual. It was the kind of breach people talked about for months — mostly because nothing like it had happened before, at least not at that scale or profile.
For a while after that, things stayed relatively quiet on this front. Supply chain attacks existed, but they were sporadic enough that most everyday users never really had to think about them.
AI Changed the Game — Fast
Then came the widespread adoption of AI tools, and the cybersecurity landscape shifted in a hurry. AI gave bad actors the ability to dramatically increase both the speed and scale of their attacks. What once required significant time and resources became far more accessible, and the effects have been visible across the board.
For a long time, the most common target was browser extensions. A dodgy extension would do exactly what it advertised — block ads, manage passwords, whatever — while also running shady operations in the background. On the lighter end of the harm spectrum, affiliate links in your browser could get quietly redirected. On the worse end, your email credentials or banking login could be stolen, or your machine could end up hosting malware you didn't know was there.
But that was then. Now, all kinds of software is getting hit — not just browser extensions. In 2025 alone, malware hidden inside games downloaded from Steam made the news multiple times. And Notepad++, a text editor that's been a staple of developers and power users for decades, ended up pushing malicious updates to existing installations. Notepad++. A tool people have trusted for years.
The Three Ways Attackers Get In
So how does a legitimate app end up distributing malware? There are a few common routes, and honestly, some of them are pretty unsettling.
The most straightforward approach is to hack the developer directly — usually by stealing or guessing their login credentials. Once an attacker has access to the developer's account or build system, they can tamper with updates before they ever reach users.
The second method is arguably more disturbing: buying access outright from the developer. Yes, that's a real thing. Someone who built a popular app decides to sell access — or sell the app itself — to a bad actor, who then uses that trusted distribution channel to push malware to an unsuspecting user base.
The third method is what security researchers call a supply chain attack, and it's how Notepad++ got caught up in all this. Rather than targeting the developer directly, attackers compromise a third-party tool or service that the developer relies on — in Notepad++'s case, a third-party update tool. The developer isn't even aware anything is wrong. Their software goes out clean as far as they know, but somewhere in the pipeline, it's been tampered with.
Why Antivirus Is Still Important — Even If You're Not "Risky"
If there's one takeaway from all of this, it's that careful online behavior alone isn't enough anymore. Antivirus software isn't just for people who click on suspicious email attachments or download cracked software from sketchy websites. It's for everyone — including the cautious, the technically savvy, and the perpetually careful.
Think of it less like a safety net for reckless behavior, and more like an alarm system for your home. You don't install a home alarm because you plan to leave your doors unlocked. You install it because even locked doors aren't always enough.
A lot of people — especially those who've been around PCs long enough to remember when antivirus software made their machines crawl — disabled antivirus years ago and never turned it back on. But modern solutions, including the built-in Windows Security, have come a long way. The performance impact during normal day-to-day computing is now minimal. The old tradeoff that once made disabling it feel reasonable simply doesn't exist the way it used to.
Long-standing third-party options like Norton and McAfee have also evolved significantly. They catch and block malware before it can do serious damage, and they operate in the background without noticeably slowing things down. That combination — effective protection with minimal performance cost — makes keeping antivirus active a straightforward decision.