A Bug That Hits Nearly Every Modern Linux System
Here's something that should make any sysadmin's stomach drop: a single vulnerability — one short Python script — can hand an attacker full root access to almost every Linux distribution shipped since 2017. That's not a hypothetical worst-case scenario. That's CopyFail, and it's happening right now.
The bug, officially tracked as CVE-2026-31431, was discovered lurking in Linux kernel versions 7.0 and earlier. Researchers disclosed it to the Linux kernel security team in late March, and to their credit, a patch came out within about a week. But here's the problem with that: the patch has to trickle down through every Linux distribution that depends on the kernel, and that process is slow. Painfully slow. Slow enough that right now, a huge number of systems are still sitting exposed.
What "CopyFail" Actually Does to Your System
The name isn't just clever branding. The affected component inside the Linux kernel — the core of the operating system, the part that has virtually unrestricted access to everything on the machine — fails to copy certain data when it should. That failure corrupts sensitive kernel data, and that corruption becomes a door an attacker can walk right through.
Once inside, they're not limited-privilege guests anymore. They've got full administrator access. Root. The keys to the kingdom.
Think about what that means in a data center context. One compromised server could cascade into access across every application, every database, every system sharing that network. It's the kind of blast radius that keeps security teams up at night, and one developer described it using exactly those words — an "unusually big blast radius" that works across "nearly every modern distribution."
Which Systems Are Actually Vulnerable
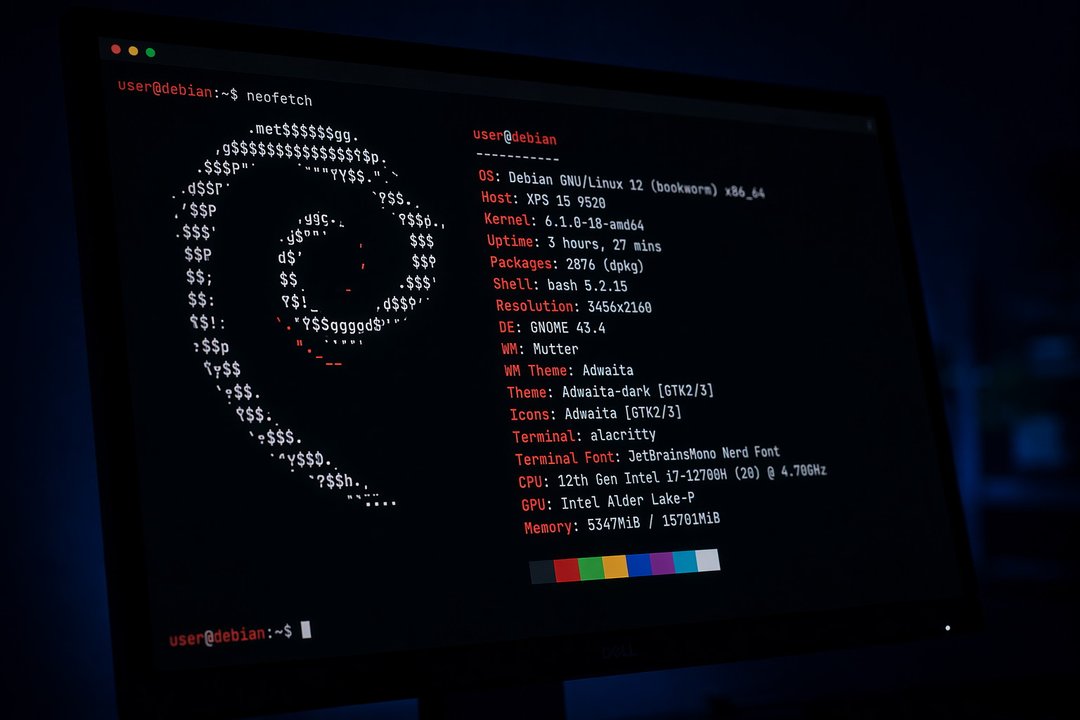
Security firm Theori, which discovered CopyFail, confirmed the vulnerability across some of the most widely deployed Linux environments out there:
- Red Hat Enterprise Linux 10.1
- Ubuntu 24.04 LTS
- Amazon Linux 2023
- SUSE 16
And it doesn't stop there. The exploit also works on Debian, Fedora, and — notably — Kubernetes, which runs on the Linux kernel. If your infrastructure touches any of these, you're in the conversation.
How Attackers Are Using It
CopyFail can't be fired at a system directly over the internet on its own — it needs local access or needs to be chained with another vulnerability that can be delivered remotely. But don't let that give you too much comfort.
Per Microsoft's security analysis, if CopyFail gets chained with an internet-facing exploit, an attacker can use the combination to achieve full root access on an affected server. And there's more than one path in:
- A regular user on a vulnerable Linux machine could be tricked into clicking a malicious link or opening a bad attachment — game over.
- Supply chain attacks are also on the table, where attackers compromise an open source developer's account and slip malicious code into a project that then gets distributed to thousands of systems.
The U.S. government confirmed that CopyFail is already being used in active malicious campaigns, which means this isn't theoretical anymore. The exploit code is public, and people are using it.
The Government Response and Patch Deadlines
CISA — the U.S. Cybersecurity and Infrastructure Security Agency — has added CopyFail to its Known Exploited Vulnerabilities catalog and issued a direct order: all civilian federal agencies must patch affected systems by May 15. That's a tight window, and it signals how seriously the government is treating this one.
Linux runs a significant chunk of the world's data centers and enterprise infrastructure. The exposure here isn't niche — it's broad, deep, and the clock is ticking.