Axios NPM Compromise Overview
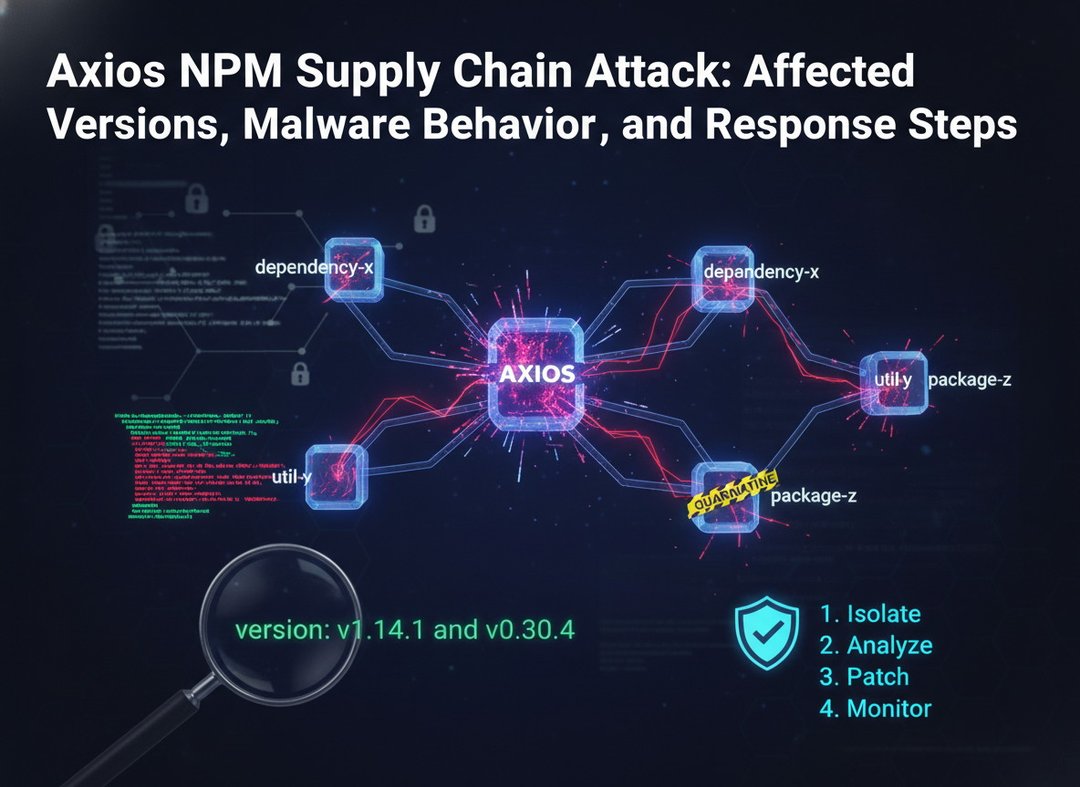
An unknown threat actor compromised the npm account of an axios maintainer and published two malicious package versions: v1.14.1 and v0.30.4. These releases introduced a dependency on a trojanized package, plain-crypto-js.
The malicious versions were removed within a few hours, but axios’s broad adoption created rapid exposure. Axios is present in roughly 80% of cloud and code environments and sees about 100 million downloads per week. Even with that short exposure window, execution was observed in 3% of affected environments.
The affected versions are tracked as GHSA-fw8c-xr5c-95f9 and MAL-2026-2306.
Malicious Axios Versions and Trojanized Dependency
The compromised axios releases differed from legitimate versions by adding a dependency on plain-crypto-js, a trojanized package. These versions were published directly through a compromised maintainer account and later removed from npm after disclosure.
That small change mattered. A short-lived package compromise can still spread quickly when the package is heavily used across development, build, and production environments.
How the Malware Works
Stage 1: Package Installation Behavior
The malicious package contains a dropper named setup.js. Its job is to download and execute platform-specific second-stage payloads from sfrclak.com:8000.
After doing that, it attempts to clean up after itself by deleting itself and restoring a clean package.json.
Stage 2: Remote Access Trojan Activity
The second-stage payloads act as lightweight remote access trojans. They beacon to the command-and-control server every 60 seconds, send system inventory information, and wait for commands.
Across operating systems, the payloads provide similar capabilities, including:
- Remote shell execution
- Binary injection
- Directory browsing
- Process listing
- System reconnaissance
Platform-Specific Payload Details
macOS Payload
On macOS, the second-stage payload is a C++ compiled Mach-O universal binary. It can also self-sign injected payloads through codesign.
Windows Payload
On Windows, the payload is delivered as a PowerShell script. It establishes persistence through a registry Run key named MicrosoftUpdate and uses a re-download batch file.
Linux Payload
On Linux, the payload is delivered as a Python script.
What Security Teams Should Do
Audit Axios Usage
Identify whether 1.14.1 or 0.30.4 was downloaded or executed anywhere in your environment. Remove any malicious artifacts from endpoints, build systems, and production workloads immediately.
Rotate Potentially Exposed Credentials
If there is any sign the malicious packages were executed, assume credentials may have been compromised. Scan affected systems for secrets such as environment variables, API keys, and tokens, then rotate them.
Investigate Possible Compromise Paths
Review build pipelines and developer machines for signs of unauthorized access or persistence. The malware runs during installation, which means it may create an upstream supply chain risk.
Monitor for Suspicious Network and Process Activity
Watch for outbound connections to sfrclak.com:8000. Review logs for beaconing behavior, unusual HTTP POST requests, and unexpected process execution linked to package installation.
Indicators of Compromise
Compromised and Malicious Packages
|
Indicator
|
Details
|
Hash
|
|
|
Stage 1, npm package
|
|
|
|
Stage 1, npm package
|
|
|
|
Stage 1.5, trojanized npm package
|
|
Stage 2 Payload Files
|
Indicator
|
Details
|
Hash
|
|
|
Stage 2 (macOS), Mach-O binary
|
|
|
|
Stage 2 (Windows), PowerShell script
|
|
|
|
Stage 2 (Linux), Python script
|
|
Network Indicators
|
Indicator
|
Details
|
|
|
C2 domain
|
|
|
C2 IP
|
|
|
C2 port
|
|
|
Campaign path
|
File Paths and Artifacts
|
Indicator
|
Details
|
|
|
macOS persistence path
|
|
|
Windows artifact
|
|
|
Windows script
|
|
|
Windows script
|
|
|
Linux script
|
Related Packages and Accounts
|
Indicator
|
Details
|
|
|
Versions:
|
|
|
Version:
|
|
|
Compromised maintainer account; email changed to
|
|
|
Published
|
Risk Assessment and Detection Priorities
The key risk here is speed. The malicious versions were available only briefly, but axios’s prevalence meant limited availability still resulted in measurable execution across environments.
That means teams shouldn’t treat package removal as the end of the problem. The real question is whether those versions were downloaded or executed, and whether the installation process exposed secrets, created persistence, or opened a path into build systems or developer machines.
Q&A
Which axios versions were malicious?
The malicious versions were 1.14.1 and 0.30.4.
What dependency was added to the compromised axios releases?
The malicious releases added a dependency on the trojanized package plain-crypto-js.
What network destination should teams monitor for?
Teams should monitor for outbound connections to sfrclak.com:8000, along with related beaconing behavior and unusual HTTP POST activity.