You're tired of paying recurring fees for VPN services. You want control over your infrastructure. You need a secure way to connect your distributed team and servers without vendor lock-in.
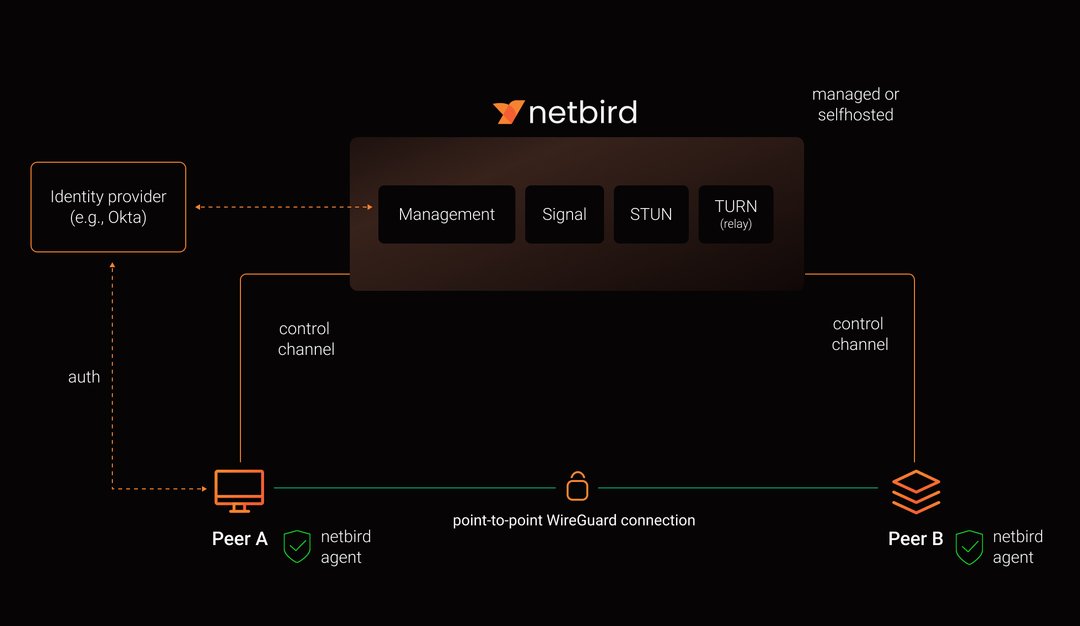
NetBird offers exactly that—a modern, open-source VPN built on Wire
Guard that you can self-host in under 15 minutes. Unlike traditional VPNs that funnel all traffic through a central server, NetBird creates peer-to-peer connections that are faster, more secure, and cost you nothing but server resources.
This guide walks you through deploying your own NetBird instance on a Linux server. By the end, you'll have a production-ready VPN that scales with your startup, not against it.
Why Self-Host NetBird?
Before we dive into the technical steps, let's talk business sense. NetBird's self-hosted option means:
- Zero per-seat costs – Your team can grow without VPN bills scaling linearly
- Data sovereignty – Authentication and connection metadata stay on your infrastructure
- Customization freedom – Integrate with your existing identity provider or security stack
- No vendor dependency – If NetBird's cloud service changes pricing or terms, you're unaffected
For early-stage founders watching burn rate, this matters. A 20-person team could save $1,200–2,400 annually compared to commercial VPN services, and that gap widens as you scale.
What You'll Need
NetBird's architecture includes five components: a management service, signal service, STUN/TURN server (Coturn), web dashboard, and an identity provider. The good news? A single installation script handles all of this.
Infrastructure requirements:
- A Linux VM with at least 1 CPU and 2GB RAM (a $6/month VPS works fine)
- A public domain name (e.g.,
vpn.yourcompany.com) - Open ports: TCP 80, 443, 33073, 10000, 33080; UDP 3478, 49152-65535
Software prerequisites:
- Docker with docker-compose plugin v2+
jqandcurl(usually pre-installed on most distributions)
If you're using AWS, DigitalOcean, Hetzner, or any cloud provider, a basic droplet or EC2 instance will work. Just ensure your firewall/security group allows the required ports.
Step 1: Prepare Your Server and Domain
First, spin up your Linux VM. Ubuntu LTS 22.04 or Debian 12 are solid choices for stability.
Point your domain's DNS A record to your server's public IP:
vpn.yourcompany.com → 203.0.113.45
DNS propagation typically takes 5–15 minutes. You can verify with:
bash
dig vpn.yourcompany.com
Step 2: Install Docker and Dependencies
If Docker isn't already installed, grab it:
bash
curl -fsSL https://get.docker.com -o get-docker.sh
sudo sh get-docker.sh
Install the required utilities:
bash
sudo apt update
sudo apt install -y jq curl
Verify Docker is running:
bash
docker --version
docker compose version
You should see version 2.x or higher for docker compose.
Step 3: Run the NetBird Installation Script
NetBird provides a one-line installer that deploys everything with Zitadel as the identity provider. Zitadel is an open-source auth platform that handles user management, SSO, and MFA out of the box.
Set your domain as an environment variable and execute the script:
bash
export NETBIRD_DOMAIN=vpn.yourcompany.com
curl -fsSL https://github.com/netbirdio/netbird/releases/latest/download/getting-started-with-zitadel.sh | bash
The script will:
- Download the latest NetBird Docker images
- Generate SSL certificates via Let's Encrypt
- Configure Zitadel with secure defaults
- Start all services in Docker containers
This takes 3–5 minutes depending on your server's network speed.
Pro tip: If you prefer to inspect the script before running it (always a good security practice), download it first:
bash
curl -sSLO https://github.com/netbirdio/netbird/releases/latest/download/getting-started-with-zitadel.sh
cat getting-started-with-zitadel.sh # Review the contents
export NETBIRD_DOMAIN=vpn.yourcompany.com
bash getting-started-with-zitadel.sh
Step 4: Access Your NetBird Dashboard
Once the script completes, it will display admin credentials in your terminal. Save these immediately—you'll need them to log in.
Navigate to https://vpn.yourcompany.com in your browser. You'll see the NetBird login screen. Use the provided credentials to access your management dashboard.
From here, you can:
- View connected peers (devices/servers)
- Configure access control policies
- Set up network routes
- Manage DNS settings
Step 5: Connect Your First Device
On any device you want to add to your VPN, install the NetBird client. For Linux:
bash
curl -fsSL https://pkgs.netbird.io/install.sh | sh
For macOS, Windows, iOS, and Android, download the appropriate client from NetBird's installation docs.
Then authenticate the device:
bash
netbird up
This will open a browser window prompting you to log in. Once authenticated, your device joins the network and receives a private IP address.
Step 6: Add Team Members
To invite additional users, access Zitadel's admin console at https://vpn.yourcompany.com/ui/console using the same credentials.
Navigate to Users → Create New User and add team members. They'll receive login credentials and can connect their devices using the netbird up command.
If you want email-based invitations, configure an SMTP server in Zitadel's settings. This is optional but improves the user experience for non-technical team members.
Step 7: Configure Access Control (Optional but Recommended)
NetBird's access control policies let you define which peers can communicate. This is crucial if you're connecting both employee devices and production servers.
In the dashboard, go to Access Control → Create Policy. For example:
- Allow developers to access staging servers but not production
- Permit only Dev
Ops team members to SSH into production databases
- Restrict contractor access to specific application servers
These policies are enforced at the network layer, so even if a device is compromised, lateral movement is limited.
Backup and Maintenance
Your NetBird installation stores configuration in the directory where you ran the script, and databases in Docker volumes.
To back up your setup:
bash
mkdir backup
cp docker-compose.yml Caddyfile zitadel.env dashboard.env turnserver.conf management.json backup/
docker compose stop management
docker compose cp -a management:/var/lib/netbird/ backup/
docker compose start management
For Zitadel's user database, follow Cockroach backup procedures.
To upgrade NetBird:
bash
docker compose pull management dashboard signal relay
docker compose up -d --force-recreate management dashboard signal relay
Always review release notes before upgrading—breaking changes are rare but documented.
Troubleshooting Common Issues
DNS not resolving: Ensure your A record points to the correct IP and has propagated. Use nslookup vpn.yourcompany.com to verify.
Port conflicts: If you're running other services on ports 80/443, you'll need to adjust the Caddyfile or use a reverse proxy.
Firewall blocking connections: Double-check that UDP ports 3478 and 49152-65535 are open. These are critical for STUN/TURN functionality.
Can't register new users: If email verification isn't working, configure SMTP in Zitadel or use the admin console to manually create users.
What You've Built
You now have a self-hosted VPN infrastructure that:
- Connects devices peer-to-peer using WireGuard's encryption
- Scales horizontally without per-user costs
- Integrates with your existing identity management
- Gives you full control over network policies and data
For founders, this is more than a technical win—it's a strategic one. You've eliminated a recurring SaaS expense, reduced vendor risk, and built infrastructure that grows with your company rather than constraining it.
Next Steps
Once your NetBird instance is running, consider:
- Integrating with your existing IdP (Okta, Azure AD, Google Workspace) instead of Zitadel
- Setting up site-to-site routing to connect entire office networks or cloud VPCs
- Enabling MFA in Zitadel for additional security
- Monitoring with Prometheus/Grafana to track connection health and performance
NetBird's official documentation covers advanced configurations, including Kubernetes deployments, custom STUN/TURN servers, and high-availability setups.
The beauty of self-hosting is that you're no longer constrained by vendor roadmaps. Need a custom feature? The codebase is open-source. Want to run it in an air-gapped environment? You control the deployment. As your startup evolves, your infrastructure can evolve with it—on your terms.